Articles
Welcome to our articles page. You will find articles on various aspects of Information Security and Business Continuity promulgated here. This is done on an ongoing basis for free of cost for your education. We emphasize your cooperation to refrain from redistributing our content for commercial purposes without our prior written consent. However, you are free to use it for your personal (educational and research) purposes or to implement a certain roadmap or strategy in your organization.
We partner with CyAlpha — a Calgary-based Cyber consulting firm, to offer you the above services.
Software development for non-technical founders: Testing early and all the time
Software testing is complex and, if not done right, can rapidly lose your customers. This article discusses the different types of testing and their importance in developing a product that your customer needs.
Software development for non-technical founders: a blueprint for your journey
In this article, we discuss the high-level blueprint for your journey in developing your product in the right way. First, we start with the overview of our blueprint before discussing each component briefly in the subsequent articles. Also, we discuss some terminologies that you should be aware of when building your ideal development or engineering team.
Software development for non-technical founders: Overview
In this short series, we explore some of the complexities, pitfalls, provide some guidance on where to start, and explain different terminologies that need to be learned by the non-technical startup founders. Although we touch on ideation and validation of startup ideas, we will focus more on software development from a startup perspective.
Developing IT Disaster Recovery Plan: Documenting and operationalizing your strategy
In the last article, we discussed testing your IT Disaster Recovery strategy in detail. In addition, we discussed setting test objectives, selecting the testing method, and preparing and facilitating the testing.
In this article, we discuss documenting, presenting your strategy for approval, and operationalizing it.
Business Continuity Planning: Business Continuity vs. Disaster Recovery
Business Continuity and Disaster Recovery are entirely different strategies despite their similarities. Business Continuity is to ensure that the business continues executing critical business processes. Disaster Recovery outlines the processes and procedures to restore vital technology to execute those business processes.
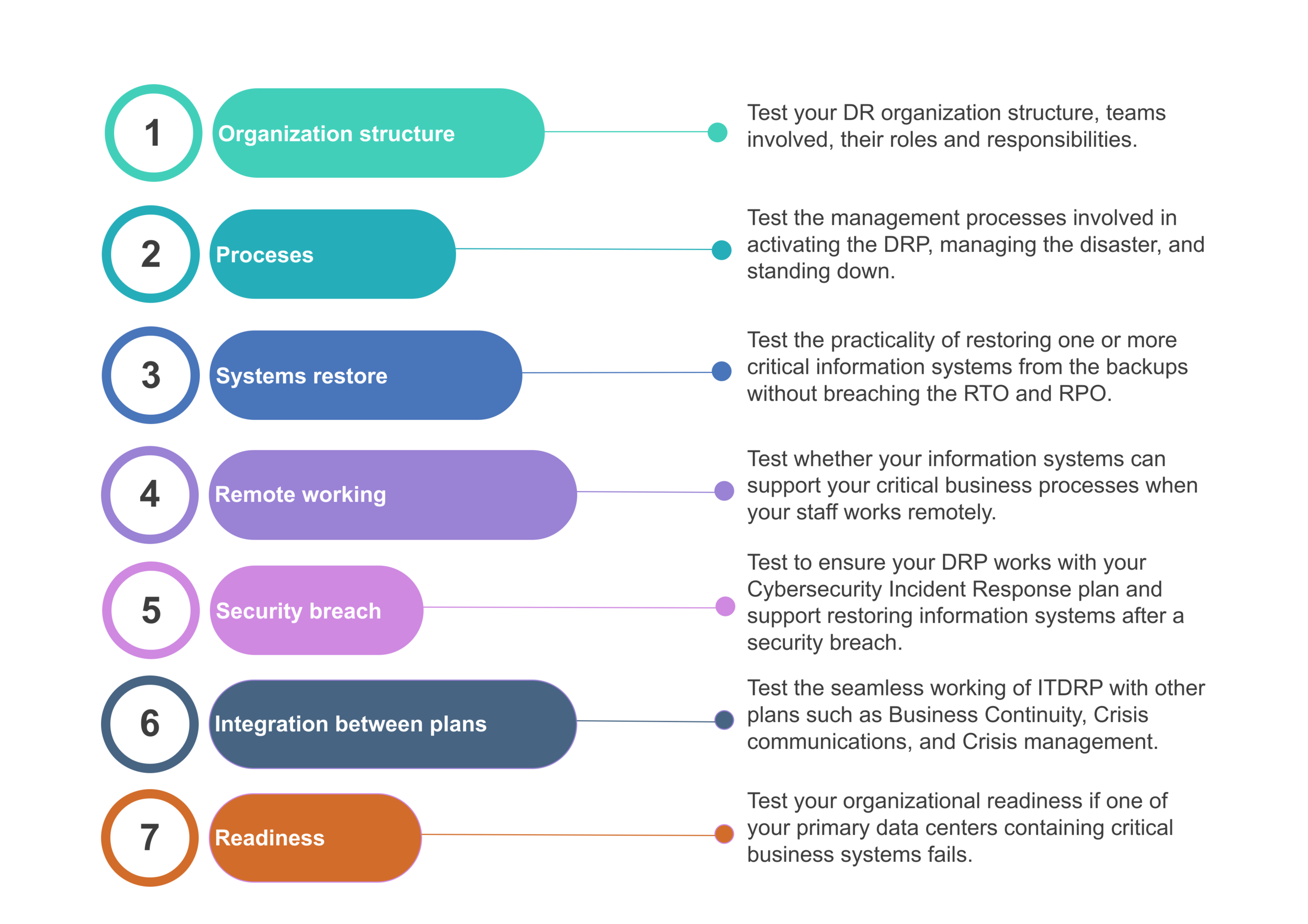
Developing IT Disaster Recovery Plan: Testing your Disaster Recovery Strategy
In this article, we discuss testing your strategy developed in the previous article. We recommend you test your DR organization structure and the management processes using a structured walkthrough and scenario-based tabletop exercise.
Developing IT Disaster Recovery Plan: Designing the recovery strategy
This article discusses the required information and the components that are part of your IT Disaster Recovery strategy.
Developing IT Disaster Recovery Plan: Conducting BIA and Risk Assessment
In the previous article, we discussed the need for documenting your organization’s IT disaster recovery plan. Then we discussed the preparation required to conduct the Business Impact Analysis (BIA). In this article, we will discuss the BIA and risk assessment.
Developing IT Disaster Recovery Plan: Introduction
93% of companies without Disaster Recovery who suffer a major data disaster are out of business within one year. Despite this statistic, the IT Disaster Recovery Plan is a crucial but often overlooked document in a business.
This article serves as an introduction to the process of documenting such a plan.
Developing Information Security Strategy: Discussing and concluding
This article concludes our InfoSec strategy series. In the DISCUSS, AGREE, and FINALIZE phases of your security strategy development, the focus is to gain widespread acceptance so that you can confidently begin implementation. This is achieved by presenting the strategy to specific segments of your organization and then tweaking as necessary. Once the strategy is approved, it’s time to develop the implementation roadmap for the year’s strategy or specific programs. And just like that, your entire organization will have peace of mind that its information is safe.