Articles
Welcome to our articles page. You will find articles on various aspects of Information Security and Business Continuity promulgated here. This is done on an ongoing basis for free of cost for your education. We emphasize your cooperation to refrain from redistributing our content for commercial purposes without our prior written consent. However, you are free to use it for your personal (educational and research) purposes or to implement a certain roadmap or strategy in your organization.
We partner with CyAlpha — a Calgary-based Cyber consulting firm, to offer you the above services.
Developing Information Security Strategy: Define your solutions
In the previous article, we discussed the ANALYZE phase. The purpose of the ANALYZE phase is to determine the context for your security strategy, identify the problem statements from each stakeholder, and list your organization’s problem patterns.
This article will discuss the DEFINE phase of our seven-step design thinking process for developing an InfoSec strategy. The goal is to define your Infosec solutions for the requirements you have identified in the previous phase.
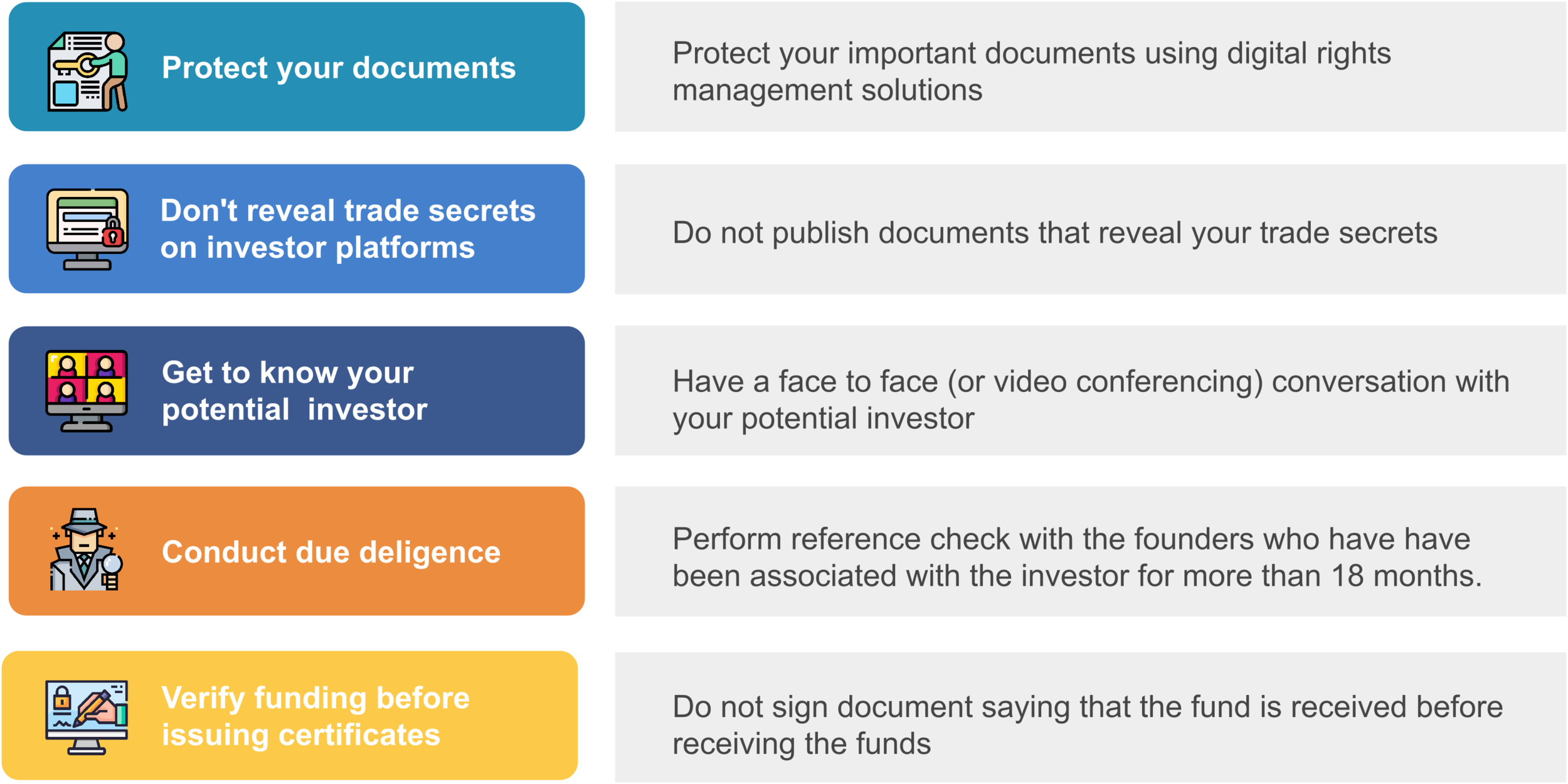
Security awareness: Five ways entrepreneurs can stay secure when fundraising
If you are a founder looking to raise funds, it is often easy to overlook the security and privacy concerns that come with this unique scenario. We have put together five recommendations to help you navigate this process securely. These recommendations will be most relevant for founders who are seeking funds from non-institutional angel investors.
Security Data Analytics and Reporting: Monitoring and reporting domains
Segregating reporting into domains helps organizations design reporting suited to each of recipients. In this article, we looked at the physical, logical and management domains at a high level. Future articles will detail the reporting viewpoints and then map stakeholders and their requirements with the reporting domains to design and deliver an SDAR system.
Security Data Analytics and Reporting: Organizational requirements
Reporting expectatoin varies depending on the owership and industry of an organization. This article will focus on how SDAR expectations and requirements differ, based on organizational type.
Security Data Analytics and Reporting: Stakeholders
The first step a business must take when implementing SDAR is to identify who its stakeholders are. Next, the business should analyze their stakeholders’ high level requirements, technology domains and viewpoints. Finally, the business can tie all this together and implement SDAR.
This article will explore the different types of stakeholders an organization can have and their respective responsibilities.
SIEM, SOAR and SDAR
SDAR is quite robust and can be a useful cybersecurity tool, even without accompanying SIEM and SOAR systems.
Security Data Analytics and Reporting: Business Expectations and value - Part 1
There are several distinct people and entities that are connected to an organization, each of which have their own unique expectations of the business. These same stakeholders also expect a convenient and secure experience when they interact with the business’ technology.